Every time someone asks me if WhatsApp is safe, I explain end-to-end encryption and I can see the lightbulb moment in their eyes. It’s a concept that sounds technical, but it’s actually quite intuitive once you get it. In 2026, with cyberattacks on the rise and digital surveillance growing, understanding what end-to-end encryption is isn’t optional anymore — it’s necessary.
Table of contents
Table of contents
- What is end-to-end encryption in simple terms
- How end-to-end encryption works technically
- Which apps use end-to-end encryption (and which don’t)
- Limitations of end-to-end encryption
- Why end-to-end encryption matters more than ever in 2026
- How to verify your app uses real end-to-end encryption
- End-to-end encryption in email and cloud storage
- FAQ: Frequently Asked Questions
- Conclusion
What is end-to-end encryption in simple terms
End-to-end encryption (E2EE) is a data protection method where only the sender and receiver can read the information. Nobody else: not your carrier, not the government, not the company running the service, not a hacker intercepting the communication. NOBODY.
Think of it this way: you send a letter inside a safe. Only you have the key to lock it and only the recipient has the key to open it. Not even the mail carrier or anyone who handles the safe can see what’s inside.
Pro-tip: Just because an app says it uses “encryption” doesn’t mean it uses end-to-end encryption. Many apps encrypt data in transit (between your phone and their servers), but the company can read it on their server. E2EE goes a step further.
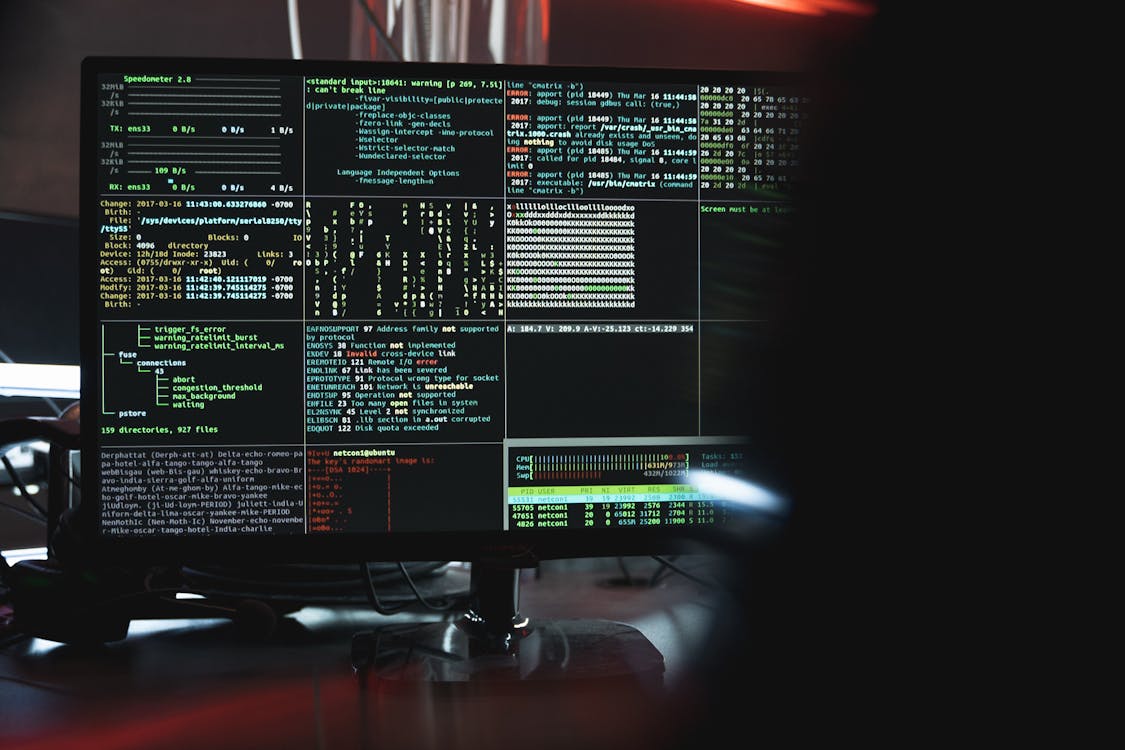
How end-to-end encryption works technically
I won’t bore you with cryptographic math, but I do want you to understand the basic process because it’s fascinating.
The process step by step
-
Key generation: When you install an app with E2EE (like Signal or WhatsApp), your device generates a key pair: a public key and a private key. The public one is shared; the private one stays only on your phone.
-
Key exchange: When you want to send a message to someone, your phone uses the recipient’s public key to encrypt the message.
-
Encrypted message sent: The message travels across the internet fully encrypted. If someone intercepts it, they see unintelligible garbage.
-
Decryption at destination: The recipient uses their private key (which only they have) to decrypt and read the message.
The crucial part: the server the message passes through never has the private keys. It can’t decrypt anything even if it wanted to.
Symmetric vs. asymmetric encryption
Modern E2EE combines two types of encryption:
- Asymmetric (public/private key): Used for the initial key exchange. It’s slow but secure for establishing the connection.
- Symmetric (single shared key): Once the connection is established, a symmetric key is used for the messages. Much faster.
The combination of both (known as Diffie-Hellman key exchange or its variants) is what makes E2EE as efficient as it is secure.
Which apps use end-to-end encryption (and which don’t)
Not all apps that claim to be secure actually use E2EE. Here’s the reality:
| App | E2EE by default | Encrypts metadata | Open source |
|---|---|---|---|
| Signal | Yes | Yes | Yes |
| Yes | No | No | |
| iMessage | Yes | Partially | No |
| Telegram | Secret chats only | No | Partially |
| Facebook Messenger | Yes (since 2023) | No | No |
| Google Messages (RCS) | Yes (between RCS users) | No | No |
| Gmail | No | No | No |
This is important: Telegram does NOT have end-to-end encryption by default. You only activate it if you create a “Secret Chat.” Regular Telegram chats are accessible by the company. Many people think Telegram is the most secure messaging app, and that’s simply not true.
Warning: End-to-end encryption protects the content of your messages, but it doesn’t always protect metadata (who you talk to, when, and how often). Signal is the only app that significantly minimizes metadata.
Limitations of end-to-end encryption
E2EE isn’t a magic solution that makes you invincible. It has important limitations:
If you lose your device without protection: Encryption is useless if someone has physical access to your unlocked phone. Always use PIN, fingerprint, or face recognition.
Unencrypted backups: If you back up WhatsApp to Google Drive without enabling backup encryption, those messages are stored unprotected. Anyone with access to your Google account could read them.
Man-in-the-middle attacks (MITM): If someone manages to impersonate the recipient during the key exchange, they could read your messages. Serious apps mitigate this with security verification (WhatsApp’s QR codes and security numbers exist for this).
Legislation and backdoors: Some governments demand companies create “backdoors” in their encryption systems. This weakens security for everyone, not just criminals as they argue.
Why end-to-end encryption matters more than ever in 2026
In recent years we’ve seen massive data breaches, ransomware attacks on hospitals and companies, and governments trying to legislate against encryption. E2EE is your best defense against:
- Hackers intercepting communications on public WiFi networks
- ISPs monitoring your traffic
- Companies collecting and selling your data
- Unauthorized access to sensitive information
It’s not paranoia, it’s common sense in a world where your data is worth gold.
How to verify your app uses real end-to-end encryption
It’s not enough for an app to claim it’s “secure.” Here’s how to check yourself whether E2EE is actually active:
In WhatsApp: Open any chat > tap the contact’s name > look for “Encryption.” You’ll see a QR code and a 60-digit number. If you and your contact scan the same code or compare numbers and they match, encryption is verified. WhatsApp also alerts you if encryption changes (which would mean someone is trying to intercept).
In Signal: Open a chat > tap the contact’s name > look for “Verify safety.” You’ll see two numeric codes that should match between both contacts. Signal has the simplest and most transparent verification implementation.
In iMessage: There’s no direct manual verification, but Apple shows an alert banner if there’s an encryption issue. For maximum security, enable Contact Key Verification in Settings > Name > Advanced.
Manual verification matters especially if you believe you could be the target of a targeted attack. For most users, the app showing that encryption is active is enough.
End-to-end encryption in email and cloud storage
E2EE isn’t exclusive to messaging apps. It also exists in other services, though with less adoption:
Email with E2EE: Traditional email is NOT E2EE. Gmail, Outlook, and most providers can read your emails. To have real encryption in email, you need to use services like ProtonMail or Tutanota, which encrypt end-to-end between users of the same service. You can also use PGP/GPG with any email client, but it’s complex to set up.
Cloud storage: Services like Tresorit, Proton Drive, and Sync.com offer E2EE for your files. This means not even the company can see your files. Google Drive, Dropbox, and OneDrive do NOT have E2EE: the company has access to your files on their servers.
Phone backups: iCloud offers E2EE for backups if you enable “Advanced Data Protection.” Google offers end-to-end encryption for Android backups, but you have to enable it manually.
Pro-tip: If privacy is a priority for you, consider switching to ProtonMail for email and Proton Drive for storage. They’re Swiss services with E2EE by default and a real commitment to privacy.
FAQ: Frequently Asked Questions
Does WhatsApp have end-to-end encryption?
Yes, WhatsApp uses the Signal protocol to encrypt all messages, calls, and video calls by default. However, Google Drive backups are not encrypted by default (you have to enable it manually).
Is end-to-end encryption 100% secure?
No system is 100% secure, but E2EE is the closest thing we have. Vulnerabilities usually sit at the endpoints (compromised devices, unencrypted backups) rather than in the encryption itself.
Can police read messages with end-to-end encryption?
Not directly. They can’t ask WhatsApp or Signal to hand over messages because technically the company can’t read them. However, if they have physical access to the unlocked device, they obviously can.
Is Signal better than WhatsApp for security?
In theory, yes. Signal is open source, minimizes metadata, and its only reason to exist is privacy. WhatsApp belongs to Meta, a company whose business model is data collection. That said, WhatsApp with E2EE is infinitely more secure than SMS or unencrypted email.
Conclusion
End-to-end encryption is the technology that protects your most private communications in the digital world. It’s not perfect or infallible, but without it, anyone could read your messages. Understanding how it works and using apps that truly implement it (Signal, WhatsApp with encrypted backups) is one of the best security decisions you can make today.
 TecnoOrange
TecnoOrange